What is Emotet Malware
Emotet malware usually appears via email, often as a part of a spam movement. An individual will have a click on the malware that will download itself to that device, and also the malicious link. It attempts to steal data and information such as victims’ wire transfer information, bank account numbers, usernames, and passwords. Its main objective is to accomplish the fake transactions to steal money from their financial accounts, victims, or redirect and intercept valid transactions.
The malicious code puts itself steadily on the device; attempt to steal login conditions by seeking the registry of device. It has also been known to use key loggers and add plug-ins to browsers, so it can not only see the stored usernames and passwords but also the information of the company as a user enters it in websites or forms.
The malware broadcasts through the network and attempts to log in and seeking for open shares and spread itself laterally to other devices.
What does Emotet Targets?
We have noticed that the Malware arrives at some company. The IT teams realize they have malware or threats; moreover, they are also aware of the improved number of account lockouts. Individuals can’t log in because the malware on their devices are trying to spread itself throughout the network by cataloging into different network nodes. It does this by trying passwords from a dictionary of common, and by reusing passwords that it learns from other devices.
For a corporation with password policies lock the accounts after several failed login attempts, that increase the lockouts that are often the first IT notification that the staff has about the Malware.
How to Save Yourself from Emotet?
Some of the simple steps are taken by the IT team to recover quickly from the Emotet.
Be Careful when you are clicking on Email links
Companies should guide the individuals to always engage themselves in good IT security practices and give the confidence to report any apprehensive activities or emails they might have seen. If the individuals make a mistake, like clicking on a malicious link, tell them to report what they did. Users want to hide a mistake and hope no one notices. But if they help to recognize an incident right away, IT staff may surround an outbreak on the network.
Allow Filtering on Traffic
As Emotet attempt to call home, it tries to set up a connection outside the boundary. If you have a filter in place to look for that type of malicious activity, they can identify, help, and also prevent malicious communication.
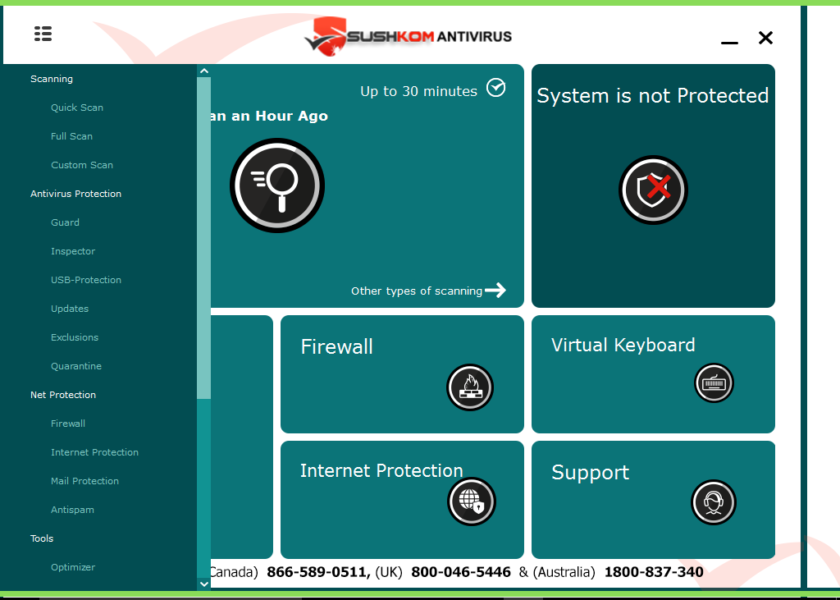
Host-Based Firewalls or Enable Internet Networks
Host-Based Firewalls come with Microsoft Windows, but some corporations either set it to be very permissive or select to turn off this function. When fully enabled, this functionality can defend an infected device from talking to another device on the network. The Emotet malware spreads this way, so preventing host-to-host communication can avoid lateral broadcast.
Monitor Account Lockouts
This is one of the telltale signs of Emotet infection. You must be always ready to respond quickly if you start to see the number of lockouts on your increased network.
Care with Financial Transactions of the device
Stealing money is one of Emotet’s primary goals. The corporation that suspects they are infected should always take extra care and verify all the confirmation numbers and wire transfers if they are transferring money.
Image credit: ZDNET